Auth Profile
Auth profiles are used to authenticate with external auth services. Currently we support Oauth2.
Register an application with Oauth provider
First register an application with an Oauth provider. You will need to provide the redirect_uri in the registered application and this should be set to ServisBot’s token broker API.
US -> https://fhums5648f.execute-api.us-east-1.amazonaws.com/us1/public/auth/v1/default-oauth2 EU -> https://jarmc7i4g4.execute-api.eu-west-1.amazonaws.com/heupper/public/auth/v1/default-oauth2
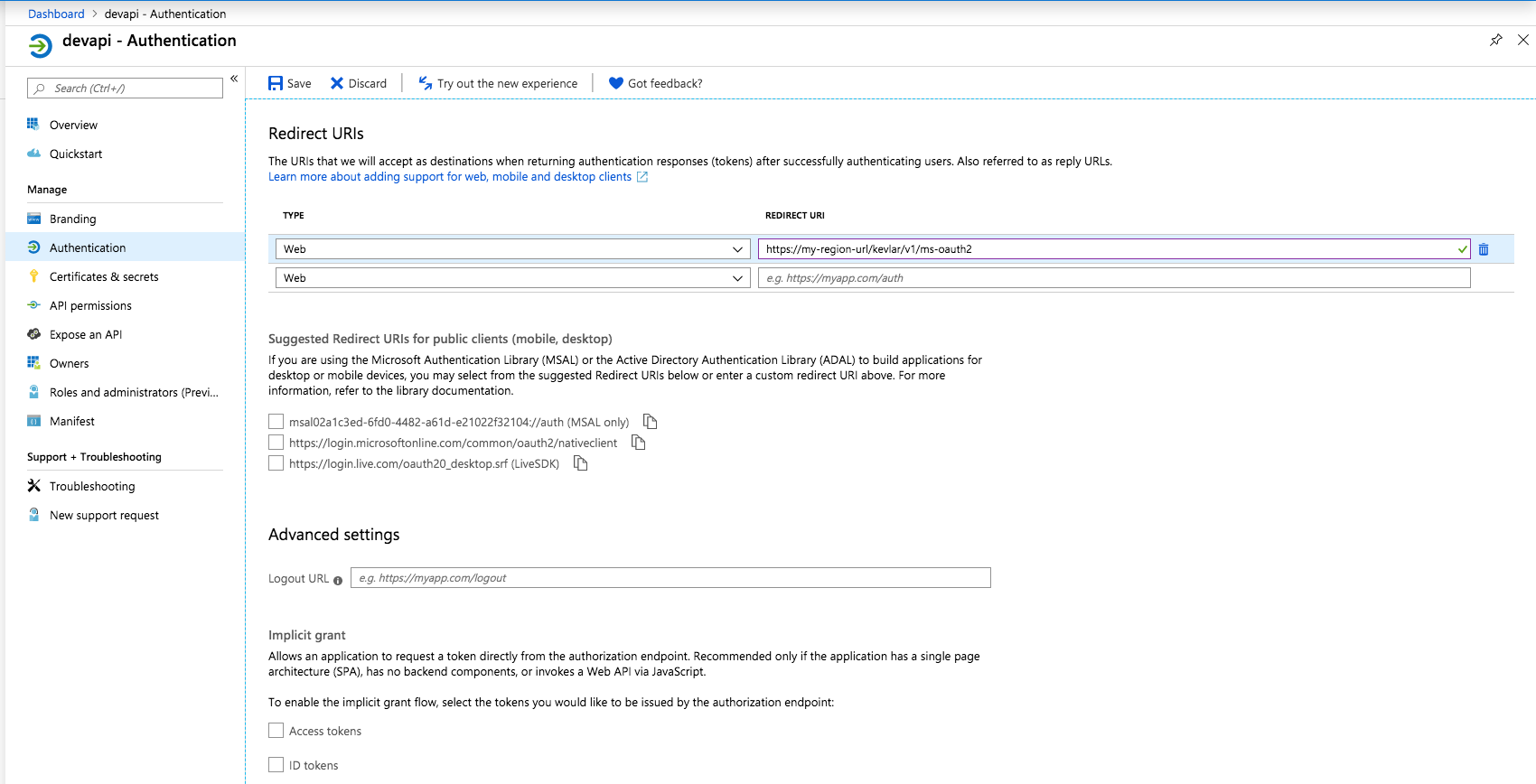
The URL token broker needs to be registered in your Application, for example, in Azure:
Create and store a secret
Create a secret in the registered application. Store the value in a ServisBot secret using the cli.
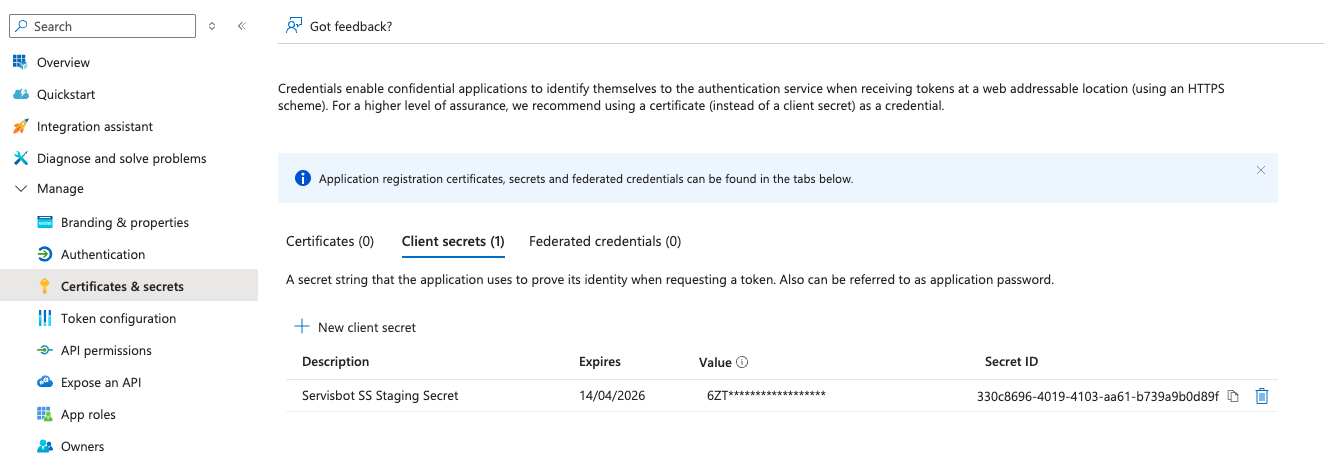
Here is an example of a secret required for Azure. Your secret SRN will be returned from the create command.
sb-cli secret create secret.json
{
"Name": "secretforoauth",
"Organization": "YOUR_ORG",
"Type": "secretdoc",
"Value": {
"secret": "6ZT**************"
}
}You will need to then run the following command in the cli.
sb-cli auth-profile create authProfile.json
authProfile.json file looks like this:
{
"Alias": "my-auth-profile",
"Type": "oauth2",
"Vendor": "default",
"Configuration": {
"RedirectUrl": "https://messenger.servisbot.com/preview.html?endpoint=flowit-endpoint",
"ClientId": "02a1c3ed-6fd0-4482-a61d-e21022f3123124",
"ClientSecret": "srn:vault::YOUR_ORG:secretdoc:secretforoauth",
"AuthenticationUrl": "https://login.microsoftonline.com/ed2ad705-5054-474a-8d7e-8b1626c12345/oauth2/authorize",
"AccessUrl": "https://login.microsoftonline.com/ed2ad705-5054-474a-8d7e-8b1626c12345/oauth2/token"
}
}You will need to use the following URLs from the Oauth provider authentication section once your application has been registered:
Redirect Url
This is the url where your messenger is hosted. We will redirect to this page once the oauth handshake has completed, and the secure session userToken will be in the url params.
Note that the RedirectUrl is not the OAuth2 redirect_uri. The redirect_uri in the registered application should be set to ServisBot’s token broker API provided above.
Authentication Url
This is the url that the user needs to oauth against which is provided along with the Access Url in the Endpoints section of the Oauth provider. This returns the authentication token to the redirect_uri mentioned above to be used to request access via oauth.
Access Url
This url is used to convert the authentication token to an access token, so we can validate the user’s session.
Using BAAS with Auth Profiles
Setup using the cli.
An alias needs to be created in the BAAS, using the following command:
sb-cli baas create baas.json
baas.json file looks like this:
{
"Alias": "authenticatedBAAS",
"Body": {},
"Endpoint": "http://www.endpoint.com",
"Headers": {},
"Method": "POST",
"RequestMapping": {},
"ResponseMapping": {},
"AuthProfile": "ProfileName" // Use your profile name here
}The BAAS connector in this case requires the Secure Session UUID generated by Servisbot to be passed as context in a variable called SecureSessionToken when executing a BAAS. For more information about passing a variable during execution see: Getting Started BAAS
BAAS Canvas Node
The node in the canvas will automatically add the SecureSessionToken context to a BAAS invocation provided that when the BAAS was selected in the node the AuthProfile was already applied to the respective BAAS.
If the AuthProfile is added afterwards you will need to reselect the BAAS in the node and save/deploy the flow.
If the AuthProfile changes after the BAAS has been selected, no changes are required.
Types
The supported AuthProfile types are:
- oauth2
oauth2
When using an oauth2 auth profile with a BAAS, an ‘Authorization’ header is automatically added containing the AccessToken that was retrieved during the secure session login process.